这篇教程指导你如何完美安装配置ubuntu 服务器版本,并安装配置一般的服务:
apache (ssl) positfix 邮件服务器 smtp-auth tls bind dns服务器,proftpd ftp服务器
mysql数据库 courierpop3/imap 邮件服务, 磁盘限额,防火墙等等。虽然这篇教程
是在32位的ubutnu 8.04上安装的,但应该也适用于64位版本的。下面是相关软件的版本:
* Web 服务器: Apache 2.2 PHP 5.2.4? Ruby
* Database 服务器: MySQL 5.0
* Mail 服务器: Postfix
* DNS 服务器: BIND9
* FTP 服务器: proftpd
* POP3/IMAP: I will use Maildir format and therefore install Courier-POP3/Courier-IMAP.
* Webalizer 网站访问分析
安装完成之后你会有个稳定的服务器系统。
1 准备必要的东西
要安装需要准备下面的资料:
* Ubuntu 8.04 LTS 服务器版cd,
可以到这里下载: ftp://releases.ubuntu.com/releases/
* 比较快的互联网
2 注意点
在这篇教程里面服务器名叫server1.example.com ip 192.168.0.100 网关 192.168.0.1,
你的设置可能跟这个不同,替换成你需要设置的参数就可以了。
3 基本系统
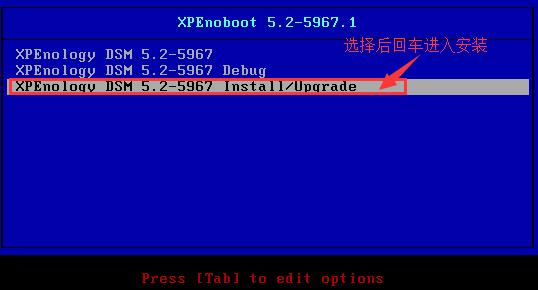
插入你的ubuntu安装关盘,从光盘启动,选择安装语言:
选择安装ubuntu服务器:
再次选择语言:
选择区域:
选择键盘 基本选择标准101键盘,或者根据你的键盘选择
安装会自动校验光盘 硬件 配置网络
输入主机名,在这个教程里面,我的主机名叫 server.example.com 所以我输入server1
下面要分区了,为了简单步骤我选择整个硬盘,你也可以选择手动分区,使用lvm卷等
选择需要分区的硬盘
当问你是否要保存硬盘改变时选择yes
然后你的心得分区就会被创建并被格式化,下面开始安装
创建一个用户比如 administrator 不要选择ubuntu保留的用户名
下面配置包安装管理器,proxy那里不要设置,除非你有使用proxy
我们需要安装dns mail lamp 服务器,但是我从来不选择他们,因为我喜欢完全控制我的系统,
只安装那些我需要的。 我们会在后面手工安装它们。唯一我选择的是openssh服务器,因为我要马上
使用ssh在安装完成后登陆。ssh可以用? PuTTY
安装继续
安装grub
基础系统就安装完成了。拿出cd重新启动系统。
进入下一步
4 启用root用户
当重启之后你可以用刚刚你设置的用户明登陆了。比如administrator。因为我们要以root用户执行下面的
步骤,所以我们现在需要启用root用户。执行下面的命令
sudo passwd root
输入一个root密码,下面我们以root执行
5 安装ssh服务器(可选)
如果你一开始没有装,这个时候你就可以装了。
apt-get install ssh openssh-server
从现在开始你就可以从你的工作台上用ssh客户端比如 PuTTY 来连接服务器执行下面的安装了。
6 安装vim-full(可选)
在这篇教程里我使用的文字编辑器是vi。缺省的vi有点奇怪的问题,要修复这个问题,我们安装vim-full
apt-get install vim-full
(你不一定非的使用vi,你也可以使用joe or nano.)
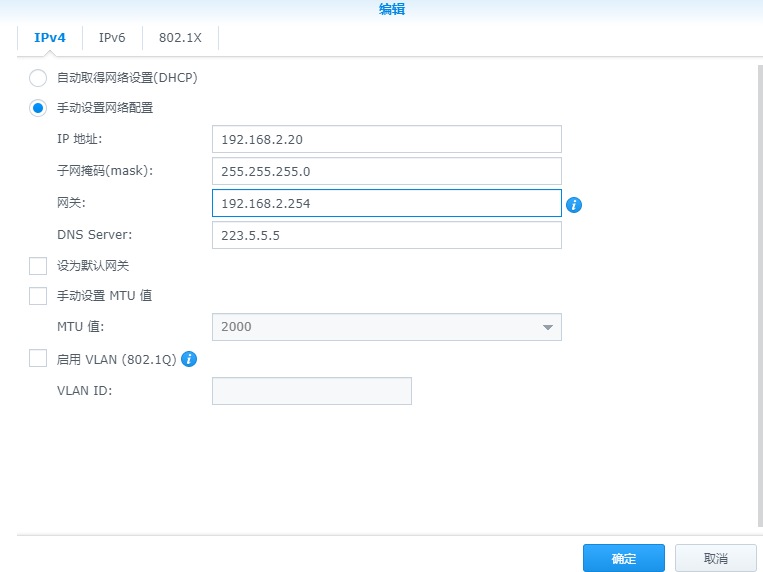
7 配置网络
我们安装时使用的是缺省配置,获得ip是使用dhcp获得的,作为一个服务器应该有一个静态 ip,编辑
/etc/network/interfaces 调整相关参数以符合你的需要,我在教程里使用的是192.168.0.100:
vi /etc/network/interfaces
# This file describes the network interfaces available on your system# and how to activate them. For more information, see interfaces(5).# The loopback network interfaceauto loiface lo inet loopback# The primary network interfaceauto eth0iface eth0 inet static address 192.168.0.100 netmask 255.255.255.0 network 192.168.0.0 broadcast 192.168.0.255 gateway 192.168.0.1
重启网络:
/etc/init.d/networking restart
编辑/etc/hosts.
vi /etc/hosts
127.0.0.1 localhost.localdomain localhost192.168.0.100 server1.example.com server1# The following lines are desirable for IPv6 capable hosts::1 ip6-localhost ip6-loopbackfe00::0 ip6-localnetff00::0 ip6-mcastprefixff02::1 ip6-allnodesff02::2 ip6-allroutersff02::3 ip6-allhosts
现在执行
echo server1.example.com > /etc/hostname
/etc/init.d/hostname.sh start
然后执行
hostname
hostname -f
两个都应该显示server1.example.com now.
8 编辑 /etc/apt/sources.list 更新安装
我这里只是举个例子,大家可以直接按照自己的需要添加互联网仓库:
vi /etc/apt/sources.list
##deb cdrom:[Ubuntu-Server 8.04 _Hardy Heron_ Release i386 (20080423.2)]/ hardy main restricted#deb cdrom:[Ubuntu-Server 8.04 _Hardy Heron_-Release i386 (20080423.2)]/ hardy main restricted# See http://help.ubuntu.com/community/UpgradeNotes for how to upgrade to# newer versions of the distribution.deb http://de.archive.ubuntu.com/ubuntu/ hardy main restricteddeb-src http://de.archive.ubuntu.com/ubuntu/ hardy main restricted## Major bug fix updates produced after the final release of the## distribution.deb http://de.archive.ubuntu.com/ubuntu/ hardy-updates main restricteddeb-src http://de.archive.ubuntu.com/ubuntu/ hardy-updates main restricted## N.B. software from this repository is ENTIRELY UNSUPPORTED by the Ubuntu## team, and may not be under a free licence. Please satisfy yourself as to## your rights to use the software. Also, please note that software in## universe WILL NOT receive any review or updates from the Ubuntu security## team.deb http://de.archive.ubuntu.com/ubuntu/ hardy universedeb-src http://de.archive.ubuntu.com/ubuntu/ hardy universedeb http://de.archive.ubuntu.com/ubuntu/ hardy-updates universedeb-src http://de.archive.ubuntu.com/ubuntu/ hardy-updates universe## N.B. software from this repository is ENTIRELY UNSUPPORTED by the Ubuntu## team, and may not be under a free licence. Please satisfy yourself as to## your rights to use the software. Also, please note that software in## multiverse WILL NOT receive any review or updates from the Ubuntu## security team.deb http://de.archive.ubuntu.com/ubuntu/ hardy multiversedeb-src http://de.archive.ubuntu.com/ubuntu/ hardy multiversedeb http://de.archive.ubuntu.com/ubuntu/ hardy-updates multiversedeb-src http://de.archive.ubuntu.com/ubuntu/ hardy-updates multiverse## Uncomment the following two lines to add software from the ‘backports’## repository.## N.B. software from this repository may not have been tested as## extensively as that contained in the main release, although it includes## newer versions of some applications which may provide useful features.## Also, please note that software in backports WILL NOT receive any review## or updates from the Ubuntu security team.# deb http://de.archive.ubuntu.com/ubuntu/ hardy-backports main restricted universe
#multiverse# deb-src http://de.archive.ubuntu.com/ubuntu/ hardy-backports main restricted universe
#multiverse## Uncomment the following two lines to add software from Canonical’s## ‘partner’ repository. This software is not part of Ubuntu, but is## offered by Canonical and the respective vendors as a service to Ubuntu## users.# deb http://archive.canonical.com/ubuntu hardy partner# deb-src http://archive.canonical.com/ubuntu hardy partnerdeb http://security.ubuntu.com/ubuntu hardy-security main restricteddeb-src http://security.ubuntu.com/ubuntu hardy-security main restricteddeb http://security.ubuntu.com/ubuntu hardy-security universedeb-src http://security.ubuntu.com/ubuntu hardy-security universedeb http://security.ubuntu.com/ubuntu hardy-security multiversedeb-src http://security.ubuntu.com/ubuntu hardy-security multiverse
接着运行更新包数据库
apt-get update
安装最新的包
apt-get upgrade
9 改变缺省的shell
/bin/sh 是一个符号链接,联结至/bin/dash, 我们比较常用的是/bin/bash, not /bin/dash. 所以我们这么做:
ln -sf /bin/bash /bin/sh
有好多脚本是用bash写的,所以,建议大家用bash作为缺省shell
10 禁用 AppArmor
AppArmor是一个安装扩展,类似红帽的selinux . 在我的观念里面,你不需要他就可以配置一个非常安全
的系统,而且这个扩展经常导致这样或那样奇怪的问题。因此我禁用了这个扩展。
像这样来禁用他:
/etc/init.d/apparmor stop
update-rc.d -f apparmor remove
apt-get remove apparmor apparmor-utils
11 安装一些相关的包
有一些包是非常通用的,建议直接装上,执行:
apt-get install binutils cpp fetchmail flex gcc libarchive-zip-perl libc6-dev libcompress-zlib-perl libdb4.3-dev
libpcre3 libpopt-dev lynx m4 make ncftp nmap openssl perl perl-modules unzip zip zlib1g-dev autoconf
automake1.9 libtool bison autotools-dev g++ build-essential
这些命令是要使用互联网链接的,如果你没有联网,可能就装不了。
12 磁盘限额
如果你使用的是一个分区,那么你一定要使用磁盘限额,以免整个系统的空间被哪个家伙全吃掉。
安装quota执行
apt-get install quota
编辑 /etc/fstab. 最起码像这样(我在/下分区上添加了,usrquota,grpquota? ):
vi /etc/fstab
# /etc/fstab: static file system information.## <file system> <mount point> <type> <options> <dump> <pass>proc /proc proc defaults 0 0# /dev/sda1UUID=6af53069-0d51-49be-b275-aeaea8d780c5 / ext3relatime,errors=remount-ro,usrquota,grpquota 0 1# /dev/sda5UUID=d8e1f66c-1442-423e-b442-8ae66eded9d7 none swap sw 0 0/dev/scd0 /media/cdrom0 udf,iso9660 user,noauto,exec,utf8 0 0/dev/fd0 /media/floppy0 auto rw,user,noauto,exec,utf8 0 0
激活quota, 执行这些命令:
touch /quota.user /quota.group
chmod 600 /quota.*
mount -o remount /
quotacheck -avugm
quotaon -avug
13 DNS 服务器
apt-get install bind9
因为一些安装问题,我们需要chrooted bind(这个相当与虚拟一个新的linux给dns使用),执行下面的步骤
/etc/init.d/bind9 stop
编辑 /etc/default/bind9 以便超级线程可以以一个没有权限的用户运行,
比如bind,chrooted 到/var/lib/named. 修改这一行: OPTIONS=”-u bind” 加上选项OPTIONS=”-u bind -t /var/lib/named”:
vi /etc/default/bind9
OPTIONS=”-u bind -t /var/lib/named”# Set RESOLVCONF=no to not run resolvconfRESOLVCONF=yes
在 /var/lib下创建相关目录:
mkdir -p /var/lib/named/etc
mkdir /var/lib/named/dev
mkdir -p /var/lib/named/var/cache/bind
mkdir -p /var/lib/named/var/run/bind/run
移动配置文件夹从/etc 到 /var/lib/named/etc:
mv /etc/bind /var/lib/named/etc
创建一个符号从旧的文件夹连接到新的配置文件夹,这是为了避免当bind升级时出现问题。
ln -s /var/lib/named/etc/bind /etc/bind
创建一些不存在的随便的设备,以修复文件夹的权限:
mknod /var/lib/named/dev/null c 1 3
mknod /var/lib/named/dev/random c 1 8
chmod 666 /var/lib/named/dev/null /var/lib/named/dev/random
chown -R bind:bind /var/lib/named/var/*
chown -R bind:bind /var/lib/named/etc/bind
我们需要修改/etc/default/syslogd 以便我们登陆系统的时候可以得到一些重要日志信息。. 修改这一行: SYSLOGD=”"? SYSLOGD=”-a /var/lib/named/dev/log”:
vi /etc/default/syslogd
## Top configuration file for syslogd### Full documentation of possible arguments are found in the manpage# syslogd(8).### For remote UDP logging use SYSLOGD=”-r”#SYSLOGD=”-a /var/lib/named/dev/log”
重启日志进程:
/etc/init.d/sysklogd restart
启动 BIND, 检查/var/log/syslog汇报的错误:
/etc/init.d/bind9 start
14 MySQL数据库
要安装MySQL, 我们执行
apt-get install mysql-server mysql-client libmysqlclient15-dev
安装中会要求你给root设置一个密码,安装完了之后,
root@localhost? 和 root@server1.example.com 该E-mail地址已受到防止垃圾邮件机器人的保护,您必须启用浏览器的Java Script才能看到。 的密码都是刚刚设的这个,我们就不需要再重设root密码了。:
New password for the MySQL “root” user: <– 你要设置的密码
Repeat password for the MySQL “root” user: <– 再输入一次你要输入的密码
我们需要mysql监听所有的接口而不是只有127.0.0.1 所以我们要编辑/etc/mysql/my.cnf
注释掉这一行 bind-address = 127.0.0.1:
vi /etc/mysql/my.cnf
[…]# Instead of skip-networking the default is now to listen only on# localhost which is more compatible and is not less secure.#bind-address = 127.0.0.1[…]
重启MySQL:
/etc/init.d/mysql restart
检查是否已经在网络上开了服务端口. 执行
netstat -tap | grep mysql
结果看起来应该象这个:
root@server1:~# netstat -tap | grep mysql
tcp??????? 0????? 0 *:mysql???????????????? *:*???????????????????? LISTEN????? 5869/mysqld
root@server1:~#
15 安装带SMTP-AUTH 和 TLS模块邮件服务器Postfix
按照下面的步骤安装daismtp-auth 和 tls 模块的邮件服务器:
apt-get install postfix libsasl2-2 sasl2-bin libsasl2-modules procmail
按照下面回答提示的两个问题:
General type of mail configuration: <– Internet Site
System mail name: <– server1.example.com
dpkg-reconfigure postfix
还会提示下面的问题:
General type of mail configuration: <– Internet Site
System mail name: <– server1.example.com
Root and postmaster mail recipient: <– [blank]
Other destinations to accept mail for (blank for none):
<– server1.example.com, localhost.example.com, localhost.localdomain, localhost
Force synchronous updates on mail queue? <– No
Local networks: <– 127.0.0.0/8
Use procmail for local delivery? <– Yes
Mailbox size limit (bytes): <– 0
Local address extension character: <– +
Internet protocols to use: <– all
接着执行下面的命令:
postconf -e ‘smtpd_sasl_local_domain =’
postconf -e ‘smtpd_sasl_auth_enable = yes’
postconf -e ‘smtpd_sasl_security_options = noanonymous’
postconf -e ‘broken_sasl_auth_clients = yes’
postconf -e ‘smtpd_sasl_authenticated_header = yes’
postconf -e ‘smtpd_recipient_restrictions = permit_sasl_authenticated,permit_mynetworks,reject_unauth_destination’
postconf -e ‘inet_interfaces = all’
echo ‘pwcheck_method: saslauthd’ >> /etc/postfix/sasl/smtpd.conf
echo ‘mech_list: plain login’ >> /etc/postfix/sasl/smtpd.conf
然后我们创建tls认证:
mkdir /etc/postfix/ssl
cd /etc/postfix/ssl/
openssl genrsa -des3 -rand /etc/hosts -out smtpd.key 1024
chmod 600 smtpd.key
openssl req -new -key smtpd.key -out smtpd.csr
openssl x509 -req -days 3650 -in smtpd.csr -signkey smtpd.key -out smtpd.crt
openssl rsa -in smtpd.key -out smtpd.key.unencrypted
mv -f smtpd.key.unencrypted smtpd.key
openssl req -new -x509 -extensions v3_ca -keyout cakey.pem -out cacert.pem -days 3650
下面配置 TLS (确认你自己使用正确的 hostname 在 myhostname这一项上):
postconf -e ‘myhostname = server1.example.com’
postconf -e ‘smtpd_tls_auth_only = no’
postconf -e ‘smtp_use_tls = yes’
postconf -e ‘smtpd_use_tls = yes’
postconf -e ‘smtp_tls_note_starttls_offer = yes’
postconf -e ‘smtpd_tls_key_file = /etc/postfix/ssl/smtpd.key’
postconf -e ‘smtpd_tls_cert_file = /etc/postfix/ssl/smtpd.crt’
postconf -e ‘smtpd_tls_CAfile = /etc/postfix/ssl/cacert.pem’
postconf -e ‘smtpd_tls_loglevel = 1′
postconf -e ‘smtpd_tls_received_header = yes’
postconf -e ‘smtpd_tls_session_cache_timeout = 3600s’
postconf -e ‘tls_random_source = dev:/dev/urandom’
最后/etc/postfix/main.cf 看起来像这样:
cat /etc/postfix/main.cf
# See /usr/share/postfix/main.cf.dist for a commented, more complete version# Debian specific: Specifying a file name will cause the first# line of that file to be used as the name. The Debian default# is /etc/mailname.#myorigin = /etc/mailnamesmtpd_banner = $myhostname ESMTP $mail_name (Ubuntu)biff = no# appending .domain is the MUA’s job.append_dot_mydomain = no# Uncomment the next line to generate “delayed mail” warnings#delay_warning_time = 4hreadme_directory = no# TLS parameterssmtpd_tls_cert_file = /etc/postfix/ssl/smtpd.crtsmtpd_tls_key_file = /etc/postfix/ssl/smtpd.keysmtpd_use_tls = yessmtpd_tls_session_cache_database = btree:${data_directory}/smtpd_scachesmtp_tls_session_cache_database = btree:${data_directory}/smtp_scache# See /usr/share/doc/postfix/TLS_README.gz in the postfix-doc package for# information on enabling SSL in the smtp client.myhostname = server1.example.comalias_maps = hash:/etc/aliasesalias_database = hash:/etc/aliasesmyorigin = /etc/mailnamemydestination = server1.example.com, localhost.example.com, localhost.localdomain, localhostrelayhost =mynetworks = 127.0.0.0/8mailbox_command = procmail -a “$EXTENSION”mailbox_size_limit = 0recipient_delimiter = +inet_interfaces = allinet_protocols = allsmtpd_sasl_local_domain =smtpd_sasl_auth_enable = yessmtpd_sasl_security_options = noanonymousbroken_sasl_auth_clients = yessmtpd_sasl_authenticated_header = yessmtpd_recipient_restrictions =
permit_sasl_authenticated,permit_mynetworks,reject_unauth_destinationsmtpd_tls_auth_only = nosmtp_use_tls = yessmtp_tls_note_starttls_offer = yessmtpd_tls_CAfile = /etc/postfix/ssl/cacert.pemsmtpd_tls_loglevel = 1smtpd_tls_received_header = yessmtpd_tls_session_cache_timeout = 3600stls_random_source = dev:/dev/urandom
认证由saslauthd实现的,因为postfix是chroot运行在/var /spool/postfix/下,我们需要做一些改变使其正常工作,
mkdir -p /var/spool/postfix/var/run/saslauthd
编辑/etc/default/saslauthd 激活sslauthd. 设置 START 为yes 把OPTIONS=”-c -m /var/run/saslauthd”
改成 OPTIONS=”-c -m /var/spool/postfix/var/run/saslauthd -r”:
vi /etc/default/saslauthd
## Settings for saslauthd daemon# Please read /usr/share/doc/sasl2-bin/README.Debian for details.## Should saslauthd run automatically on startup? (default: no)START=yes# Description of this saslauthd instance. Recommended.# (suggestion: SASL Authentication Daemon)DESC=”SASL Authentication Daemon”# Short name of this saslauthd instance. Strongly recommended.# (suggestion: saslauthd)NAME=”saslauthd”# Which authentication mechanisms should saslauthd use? (default: pam)## Available options in this Debian package:# getpwent — use the getpwent() library function# kerberos5 — use Kerberos 5# pam — use PAM# rimap — use a remote IMAP server# shadow — use the local shadow password file# sasldb — use the local sasldb database file# ldap — use LDAP (configuration is in /etc/saslauthd.conf)## Only one option may be used at a time. See the saslauthd man page# for more information.## Example: MECHANISMS=”pam”MECHANISMS=”pam”# Additional options for this mechanism. (default: none)# See the saslauthd man page for information about mech-specific options.MECH_OPTIONS=”"# How many saslauthd processes should we run? (default: 5)# A value of 0 will fork a new process for each connection.THREADS=5# Other options (default: -c -m /var/run/saslauthd)# Note: You MUST specify the -m option or saslauthd won’t run!## See /usr/share/doc/sasl2-bin/README.Debian for Debian-specific information.# See the saslauthd man page for general information about these options.## Example for postfix users: “-c -m /var/spool/postfix/var/run/saslauthd”#OPTIONS=”-c -m /var/run/saslauthd”OPTIONS=”-c -m /var/spool/postfix/var/run/saslauthd -r”
下面把postfix user 加到sasl组里面,这一步使postfix有权限使用saslauthd
adduser postfix sasl
重启Postfix 启动saslauthd:
/etc/init.d/postfix restart
/etc/init.d/saslauthd start
下面看看smtp-auth 和tls工作了没:
telnet localhost 25
看到提示了后执行:
ehlo localhost
如果你看到了下面的
250-STARTTLS
还有这个
250-AUTH LOGIN PLAIN
那就证明所有的都ok了。
在我的机器上显示的像下面的:
root@server1:/etc/postfix/ssl# telnet localhost 25
Trying 127.0.0.1…
Connected to localhost.localdomain.
Escape character is ‘^]’.
220 server1.example.com ESMTP Postfix (Ubuntu)
ehlo localhost
250-server1.example.com
250-PIPELINING
250-SIZE 10240000
250-VRFY
250-ETRN
250-STARTTLS
250-AUTH LOGIN PLAIN
250-AUTH=LOGIN PLAIN
250-ENHANCEDSTATUSCODES
250-8BITMIME
250 DSN
quit
221 2.0.0 Bye
Connection closed by foreign host.
root@server1:/etc/postfix/ssl#
quit
返回系统shells.
16 安装 Courier-IMAP/Courier-POP3
执行下面的命令安装Courier-IMAP/Courier-IMAP-SSL (IMAPs 在端口 993上)
和Courier-POP3/Courier-POP3-SSL (POP3s 在端口 995上)pop3和imap是明文传输密码的,这两个包是为了解决安全问提出现的:
apt-get install courier-authdaemon courier-base courier-imap
courier-imap-ssl courier-pop courier-pop-ssl courier-ssl gamin libgamin0 libglib2.0-0
提示下面两个问题:
Create directories for web-based administration? <– No
SSL certificate required <– Ok
17 安装Apache/PHP5/Ruby
下面我们安装Apache:
apt-get install apache2 apache2-doc apache2-mpm-prefork apache2-utils libexpat1 ssl-cert
下面我们安装PHP5 和 Ruby (两个都是apache的模块):
apt-get install libapache2-mod-php5 libapache2-mod-ruby php5 php5-common php5-curl php5-dev php5-gd php5-idn php-pear php5-imagick php5-imap php5-json php5-mcrypt php5-memcache php5-mhash php5-ming php5-mysql php5-pspell php5-recode php5-snmp php5-sqlite php5-tidy php5-xmlrpc php5-xsl
编辑edit /etc/apache2/mods-available/dir.conf:
vi /etc/apache2/mods-available/dir.conf
更改DirectoryIndex 这一行:
<IfModule mod_dir.c>#DirectoryIndex index.html index.cgi index.pl index.php index.xhtml index.htmDirectoryIndex index.html index.htm index.shtml index.cgi index.php </IfModule>
现在我们可以激活某些Apache 模块了 (SSL, rewrite, suexec, and include):
a2enmod ssl
a2enmod rewrite
a2enmod suexec
a2enmod include
重新加载配置文件:
/etc/init.d/apache2 force-reload
17Proftpd
安装Proftpd, run
apt-get install proftpd ucf
会提示你这个问题:
Run proftpd: <– standalone
为了提高proftpd的安全性可以做下面的操作,更多信息可以看这里: http://proftpd.org/localsite/Userguide/linked/userguide.html):
vi /etc/proftpd/proftpd.conf
[…]DefaultRoot ~IdentLookups offServerIdent on “FTP Server ready.”[…]
18 网站访问统计分析
安装webalizer,直接运行
apt-get install webalizer
19 同步系统时钟
与互联网上某个时间服务器同步是一个不错的选择。简单的执行
apt-get install ntp ntpdate
以后你的系统时间就会自动同步了。
原文链接:https://blog.csdn.net/centaury_xu/article/details/7305224