素材来源:华为防火墙配置指南
一边学习一边整理试验笔记,并与大家分享,侵权即删,谢谢支持!
附上汇总贴:玩转华为ENSP模拟器系列 | 合集_COCOgsta的博客-CSDN博客_华为模拟器实验
目标
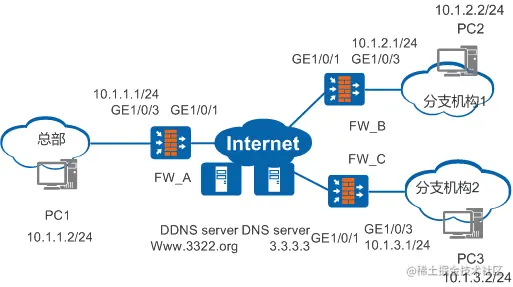
分支机构通过IPSec隧道连接总部。由于总部和分支都通过PPPoE拨号获取IP地址,每次获取到的IP地址不同。因此总部为方便分支机构接入,需要配置DDNS功能,使分支机构通过域名接入总部。
组网需求
如图1所示,某企业分为总部(HQ)和两个分支机构(Branch 1和Branch 2)。组网如下:
- 分支机构1和分支机构2分别通过FW_B和FW_C与Internet相连。
- FW_A和FW_B、FW_A和FW_C相互路由可达。
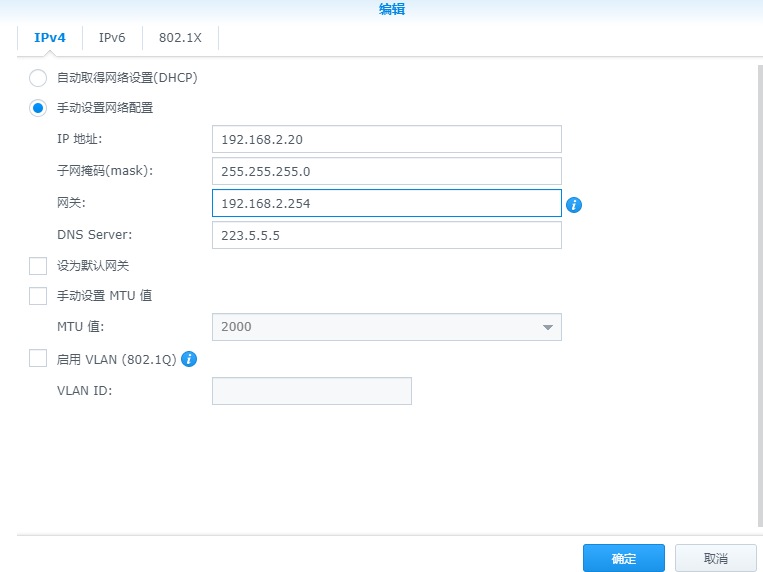
- 总部和分支机构均通过PPPoE拨号上网。且内网设备均通过DHCP方式从FW接口获取IP地址。
- 总部网关支持DDNS功能,分支网关支持DNS功能。总部域名固定。
要求实现如下需求:
- 分支机构PC2、PC3能与总部PC1之间进行安全通信。
- FW_A、FW_B以及FW_A、FW_C之间分别建立IPSec隧道。FW_B、FW_C不直接建立任何IPSec连接。
配置思路
- 隧道两端设备分别配置PPPoE拨号,实现设备上网。
- 总部采用模板方式IPSec安全策略,以响应多个分支机构的需求;分支机构采用配置ISAKMP方式IPSec安全策略。
- 分支机构要访问总部设备,需要在FW_A上开启域名解析以及DDNS策略,以便将获取的IP地址与网络中的DNS服务器中的域名建立对应关系,并及时更新。
操作步骤
-
在FW_A上配置DHCP和PPPoE客户端。
- 配置GE1/0/3接口,开启DHCP,对内网用户自动分配IP地址。
-
<sysname> system-view [sysname] sysname FW_A [FW_A] interface gigabitethernet 1 / 0 / 3 [FW_A-GigabitEthernet1/0/3] ip address 10.1.1.1 24 [FW_A-GigabitEthernet1/0/3] dhcp select interface [FW_A-GigabitEthernet1/0/3] quit [FW_A] firewall zone trust [FW_A-zone-trust] add interface gigabitethernet 1 / 0 / 3 [FW_A-zone-trust] quit 复制代码
<sysname> system-view [sysname] sysname FW_A [FW_A] interface gigabitethernet 1 / 0 / 3 [FW_A-GigabitEthernet1/0/3] ip address 10.1.1.1 24 [FW_A-GigabitEthernet1/0/3] dhcp select interface [FW_A-GigabitEthernet1/0/3] quit [FW_A] firewall zone trust [FW_A-zone-trust] add interface gigabitethernet 1 / 0 / 3 [FW_A-zone-trust] quit 复制代码
<sysname> system-view [sysname] sysname FW_A [FW_A] interface gigabitethernet 1 / 0 / 3 [FW_A-GigabitEthernet1/0/3] ip address 10.1.1.1 24 [FW_A-GigabitEthernet1/0/3] dhcp select interface [FW_A-GigabitEthernet1/0/3] quit [FW_A] firewall zone trust [FW_A-zone-trust] add interface gigabitethernet 1 / 0 / 3 [FW_A-zone-trust] quit 复制代码 - 配置PPPoE Client。
-
[FW_A] dialer-rule 10 ip permit [FW_A] interface Dialer 1 [FW_A-Dialer1] dialer user dialeruser [FW_A-Dialer1] dialer bundle 5 [FW_A-Dialer1] dialer-group 10 [FW_A-Dialer1] ip address ppp-negotiate [FW_A-Dialer1] ppp chap user dialeruser [FW_A-Dialer1] ppp chap password cipher Hello123 [FW_A-Dialer1] quit [FW_A] firewall zone untrust [FW_A-zone-untrust] add interface Dialer 1 [FW_A-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_A-zone-untrust] quit [FW_A] interface gigabitethernet 1 / 0 / 1 [FW_A-GigabitEthernet1/0/1] pppoe-client dial-bundle-number 5 [FW_A-GigabitEthernet1/0/1] quit 复制代码
[FW_A] dialer-rule 10 ip permit [FW_A] interface Dialer 1 [FW_A-Dialer1] dialer user dialeruser [FW_A-Dialer1] dialer bundle 5 [FW_A-Dialer1] dialer-group 10 [FW_A-Dialer1] ip address ppp-negotiate [FW_A-Dialer1] ppp chap user dialeruser [FW_A-Dialer1] ppp chap password cipher Hello123 [FW_A-Dialer1] quit [FW_A] firewall zone untrust [FW_A-zone-untrust] add interface Dialer 1 [FW_A-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_A-zone-untrust] quit [FW_A] interface gigabitethernet 1 / 0 / 1 [FW_A-GigabitEthernet1/0/1] pppoe-client dial-bundle-number 5 [FW_A-GigabitEthernet1/0/1] quit 复制代码
[FW_A] dialer-rule 10 ip permit [FW_A] interface Dialer 1 [FW_A-Dialer1] dialer user dialeruser [FW_A-Dialer1] dialer bundle 5 [FW_A-Dialer1] dialer-group 10 [FW_A-Dialer1] ip address ppp-negotiate [FW_A-Dialer1] ppp chap user dialeruser [FW_A-Dialer1] ppp chap password cipher Hello123 [FW_A-Dialer1] quit [FW_A] firewall zone untrust [FW_A-zone-untrust] add interface Dialer 1 [FW_A-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_A-zone-untrust] quit [FW_A] interface gigabitethernet 1 / 0 / 1 [FW_A-GigabitEthernet1/0/1] pppoe-client dial-bundle-number 5 [FW_A-GigabitEthernet1/0/1] quit 复制代码 - 配置Trust域与Untrust域之间的域间安全策略。
-
[FW_A] security-policy [FW_A-policy-security] rule name policy1 [FW_A-policy-security-rule-policy1] source-zone trust [FW_A-policy-security-rule-policy1] destination-zone untrust [FW_A-policy-security-rule-policy1] source-address 10.1.1.0 24 [FW_A-policy-security-rule-policy1] destination-address 10.1.2.0 24 [FW_A-policy-security-rule-policy1] destination-address 10.1.3.0 24 [FW_A-policy-security-rule-policy1] action permit [FW_A-policy-security-rule-policy1] quit [FW_A-policy-security] rule name policy2 [FW_A-policy-security-rule-policy2] source-zone untrust [FW_A-policy-security-rule-policy2] destination-zone trust [FW_A-policy-security-rule-policy2] source-address 10.1.2.0 24 [FW_A-policy-security-rule-policy2] source-address 10.1.3.0 24 [FW_A-policy-security-rule-policy2] destination-address 10.1.1.0 24 [FW_A-policy-security-rule-policy2] action permit [FW_A-policy-security-rule-policy2] quit 复制代码
[FW_A] security-policy [FW_A-policy-security] rule name policy1 [FW_A-policy-security-rule-policy1] source-zone trust [FW_A-policy-security-rule-policy1] destination-zone untrust [FW_A-policy-security-rule-policy1] source-address 10.1.1.0 24 [FW_A-policy-security-rule-policy1] destination-address 10.1.2.0 24 [FW_A-policy-security-rule-policy1] destination-address 10.1.3.0 24 [FW_A-policy-security-rule-policy1] action permit [FW_A-policy-security-rule-policy1] quit [FW_A-policy-security] rule name policy2 [FW_A-policy-security-rule-policy2] source-zone untrust [FW_A-policy-security-rule-policy2] destination-zone trust [FW_A-policy-security-rule-policy2] source-address 10.1.2.0 24 [FW_A-policy-security-rule-policy2] source-address 10.1.3.0 24 [FW_A-policy-security-rule-policy2] destination-address 10.1.1.0 24 [FW_A-policy-security-rule-policy2] action permit [FW_A-policy-security-rule-policy2] quit 复制代码
[FW_A] security-policy [FW_A-policy-security] rule name policy1 [FW_A-policy-security-rule-policy1] source-zone trust [FW_A-policy-security-rule-policy1] destination-zone untrust [FW_A-policy-security-rule-policy1] source-address 10.1.1.0 24 [FW_A-policy-security-rule-policy1] destination-address 10.1.2.0 24 [FW_A-policy-security-rule-policy1] destination-address 10.1.3.0 24 [FW_A-policy-security-rule-policy1] action permit [FW_A-policy-security-rule-policy1] quit [FW_A-policy-security] rule name policy2 [FW_A-policy-security-rule-policy2] source-zone untrust [FW_A-policy-security-rule-policy2] destination-zone trust [FW_A-policy-security-rule-policy2] source-address 10.1.2.0 24 [FW_A-policy-security-rule-policy2] source-address 10.1.3.0 24 [FW_A-policy-security-rule-policy2] destination-address 10.1.1.0 24 [FW_A-policy-security-rule-policy2] action permit [FW_A-policy-security-rule-policy2] quit 复制代码 - 配置Untrust域与Local域之间的域间安全策略。
-
[FW_A-policy-security] rule name policy3 [FW_A-policy-security-rule-policy3] source-zone local [FW_A-policy-security-rule-policy3] destination-zone untrust [FW_A-policy-security-rule-policy3] action permit [FW_A-policy-security-rule-policy3] quit [FW_A-policy-security] rule name policy4 [FW_A-policy-security-rule-policy4] source-zone untrust [FW_A-policy-security-rule-policy4] destination-zone local [FW_A-policy-security-rule-policy4] action permit [FW_A-policy-security-rule-policy4] quit [FW_A-policy-security] quit 复制代码
[FW_A-policy-security] rule name policy3 [FW_A-policy-security-rule-policy3] source-zone local [FW_A-policy-security-rule-policy3] destination-zone untrust [FW_A-policy-security-rule-policy3] action permit [FW_A-policy-security-rule-policy3] quit [FW_A-policy-security] rule name policy4 [FW_A-policy-security-rule-policy4] source-zone untrust [FW_A-policy-security-rule-policy4] destination-zone local [FW_A-policy-security-rule-policy4] action permit [FW_A-policy-security-rule-policy4] quit [FW_A-policy-security] quit 复制代码
[FW_A-policy-security] rule name policy3 [FW_A-policy-security-rule-policy3] source-zone local [FW_A-policy-security-rule-policy3] destination-zone untrust [FW_A-policy-security-rule-policy3] action permit [FW_A-policy-security-rule-policy3] quit [FW_A-policy-security] rule name policy4 [FW_A-policy-security-rule-policy4] source-zone untrust [FW_A-policy-security-rule-policy4] destination-zone local [FW_A-policy-security-rule-policy4] action permit [FW_A-policy-security-rule-policy4] quit [FW_A-policy-security] quit 复制代码 - 配置到达分支机构的静态路由。
-
[FW_A] ip route- static 0.0.0.0 0.0.0.0 Dialer1 复制代码
[FW_A] ip route- static 0.0.0.0 0.0.0.0 Dialer1 复制代码
[FW_A] ip route- static 0.0.0.0 0.0.0.0 Dialer1 复制代码
-
在FW_A上配置IPSec策略组,并在接口上应用IPSec策略组。
- 定义被保护的数据流。
-
[FW_A] acl 3000 [FW_A-acl-adv-3000] rule permit ip source 10.1.0.0 0.0.255.255 destination 10.1.2.0 0.0.0.255 [FW_A-acl-adv-3000] rule permit ip source 10.1.0.0 0.0.255.255 destination 10.1.3.0 0.0.0.255 [FW_A-acl-adv-3000] quit 复制代码
[FW_A] acl 3000 [FW_A-acl-adv-3000] rule permit ip source 10.1.0.0 0.0.255.255 destination 10.1.2.0 0.0.0.255 [FW_A-acl-adv-3000] rule permit ip source 10.1.0.0 0.0.255.255 destination 10.1.3.0 0.0.0.255 [FW_A-acl-adv-3000] quit 复制代码
[FW_A] acl 3000 [FW_A-acl-adv-3000] rule permit ip source 10.1.0.0 0.0.255.255 destination 10.1.2.0 0.0.0.255 [FW_A-acl-adv-3000] rule permit ip source 10.1.0.0 0.0.255.255 destination 10.1.3.0 0.0.0.255 [FW_A-acl-adv-3000] quit 复制代码 - 配置IPSec安全提议。采用默认参数。
-
[FW_A] ipsec proposal tran1 [FW_A-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_A-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_A-ipsec-proposal-tran1] quit 复制代码
[FW_A] ipsec proposal tran1 [FW_A-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_A-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_A-ipsec-proposal-tran1] quit 复制代码
[FW_A] ipsec proposal tran1 [FW_A-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_A-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_A-ipsec-proposal-tran1] quit 复制代码 - 配置IKE安全提议。采用默认参数。
-
[FW_A] ike proposal 10 [FW_A-ike-proposal-10] authentication-method pre-share [FW_A-ike-proposal-10] prf hmac-sha2- 256 [FW_A-ike-proposal-10] encryption-algorithm aes- 256 [FW_A-ike-proposal-10] dh group2 [FW_A-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_A-ike-proposal-10] quit 复制代码
[FW_A] ike proposal 10 [FW_A-ike-proposal-10] authentication-method pre-share [FW_A-ike-proposal-10] prf hmac-sha2- 256 [FW_A-ike-proposal-10] encryption-algorithm aes- 256 [FW_A-ike-proposal-10] dh group2 [FW_A-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_A-ike-proposal-10] quit 复制代码
[FW_A] ike proposal 10 [FW_A-ike-proposal-10] authentication-method pre-share [FW_A-ike-proposal-10] prf hmac-sha2- 256 [FW_A-ike-proposal-10] encryption-algorithm aes- 256 [FW_A-ike-proposal-10] dh group2 [FW_A-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_A-ike-proposal-10] quit 复制代码 - 配置IKE Peer。
-
[FW_A] ike peer b [FW_A-ike-peer-b] ike-proposal 10 [FW_A-ike-peer-b] pre-shared-key Test ! 1234 [FW_A-ike-peer-b] quit 复制代码
[FW_A] ike peer b [FW_A-ike-peer-b] ike-proposal 10 [FW_A-ike-peer-b] pre-shared-key Test ! 1234 [FW_A-ike-peer-b] quit 复制代码
[FW_A] ike peer b [FW_A-ike-peer-b] ike-proposal 10 [FW_A-ike-peer-b] pre-shared-key Test ! 1234 [FW_A-ike-peer-b] quit 复制代码 - 配置名称为map_temp序号为11的IPSec策略模板。
-
[FW_A] ipsec policy-template map_temp 11 [FW_A-ipsec-policy-templet-map_temp-1] security acl 3000 [FW_A-ipsec-policy-templet-map_temp-1] proposal tran1 [FW_A-ipsec-policy-templet-map_temp-1] ike-peer b [FW_A-ipsec-policy-templet-map_temp-1] quit 复制代码
[FW_A] ipsec policy-template map_temp 11 [FW_A-ipsec-policy-templet-map_temp-1] security acl 3000 [FW_A-ipsec-policy-templet-map_temp-1] proposal tran1 [FW_A-ipsec-policy-templet-map_temp-1] ike-peer b [FW_A-ipsec-policy-templet-map_temp-1] quit 复制代码
[FW_A] ipsec policy-template map_temp 11 [FW_A-ipsec-policy-templet-map_temp-1] security acl 3000 [FW_A-ipsec-policy-templet-map_temp-1] proposal tran1 [FW_A-ipsec-policy-templet-map_temp-1] ike-peer b [FW_A-ipsec-policy-templet-map_temp-1] quit 复制代码 - 在IPSec策略组map1的序号为20的安全策略中引用IPSec策略模板map_temp。
-
[FW_A] ipsec policy map1 20 isakmp template map_temp 复制代码
[FW_A] ipsec policy map1 20 isakmp template map_temp 复制代码
[FW_A] ipsec policy map1 20 isakmp template map_temp 复制代码 - 在接口Dialer 1上应用IPSec策略组map1。
-
[FW_A] interface Dialer 1 [FW_A-Dialer1] ipsec policy map1 [FW_A-Dialer1] quit 复制代码
[FW_A] interface Dialer 1 [FW_A-Dialer1] ipsec policy map1 [FW_A-Dialer1] quit 复制代码
[FW_A] interface Dialer 1 [FW_A-Dialer1] ipsec policy map1 [FW_A-Dialer1] quit 复制代码
- 在FW_A上配置DDNS。
开启域名解析,FW_A通过域名能访问DDNS Server。
[FW_A] dns resolve [FW_A] dns server 3.3.3.3 复制代码[FW_A] dns resolve [FW_A] dns server 3.3.3.3 复制代码[FW_A] dns resolve [FW_A] dns server 3.3.3.3 复制代码
向DDNS服务提供商申请DDNS服务。
请联系DDNS服务提供商,并根据DDNS服务提供商的说明操作。假设申请得到的用户名和密码都为:abc123;DDNS Client的域名为:www.abcd.3322.org;选择的DDNS服务提供商为:www.3322.org。
配置DDNS策略。
[FW_A] ddns policy abc [FW_A-ddns-policy-abc] method vendor-specific [FW_A-ddns-policy-abc] url http : //abc123:abc123@members.3322.org/dyndns/update?system=dyndns/update?system=dyndns&hostname=<h>&myip=<a> [FW_A-ddns-policy-abc] quit 复制代码[FW_A] ddns policy abc [FW_A-ddns-policy-abc] method vendor-specific [FW_A-ddns-policy-abc] url http : //abc123:abc123@members.3322.org/dyndns/update?system=dyndns/update?system=dyndns&hostname=<h>&myip=<a> [FW_A-ddns-policy-abc] quit 复制代码[FW_A] ddns policy abc [FW_A-ddns-policy-abc] method vendor-specific [FW_A-ddns-policy-abc] url http : //abc123:abc123@members.3322.org/dyndns/update?system=dyndns/update?system=dyndns&hostname=<h>&myip=<a> [FW_A-ddns-policy-abc] quit 复制代码
应用DDNS策略。
[FW_A] interface Dialer 1 [FW_A-Dialer1] ddns apply policy abc [FW_A-Dialer1] quit 复制代码[FW_A] interface Dialer 1 [FW_A-Dialer1] ddns apply policy abc [FW_A-Dialer1] quit 复制代码[FW_A] interface Dialer 1 [FW_A-Dialer1] ddns apply policy abc [FW_A-Dialer1] quit 复制代码
-
配置FW_B的基础配置。
-
配置GE1/0/3接口,开启DHCP,对内网用户自动分配IP地址。
-
<sysname> system-view [sysname] sysname FW_B [FW_B] gigabitethernet 1 / 0 / 3 [FW_B-GigabitEthernet1/0/3] ip address 10.1.2.1 24 [FW_B-GigabitEthernet1/0/3] dhcp select interface [FW_B-GigabitEthernet1/0/3] quit [FW_B] firewall zone trust [FW_B-zone-trust] add interface gigabitethernet 1 / 0 / 3 [FW_B-zone-trust] quit 复制代码
<sysname> system-view [sysname] sysname FW_B [FW_B] gigabitethernet 1 / 0 / 3 [FW_B-GigabitEthernet1/0/3] ip address 10.1.2.1 24 [FW_B-GigabitEthernet1/0/3] dhcp select interface [FW_B-GigabitEthernet1/0/3] quit [FW_B] firewall zone trust [FW_B-zone-trust] add interface gigabitethernet 1 / 0 / 3 [FW_B-zone-trust] quit 复制代码
<sysname> system-view [sysname] sysname FW_B [FW_B] gigabitethernet 1 / 0 / 3 [FW_B-GigabitEthernet1/0/3] ip address 10.1.2.1 24 [FW_B-GigabitEthernet1/0/3] dhcp select interface [FW_B-GigabitEthernet1/0/3] quit [FW_B] firewall zone trust [FW_B-zone-trust] add interface gigabitethernet 1 / 0 / 3 [FW_B-zone-trust] quit 复制代码 - 配置PPPoE Client。
-
[FW_B] dialer-rule 10 ip permit [FW_B] interface Dialer 1 [FW_B-Dialer1] dialer user dialeruser [FW_B-Dialer1] dialer bundle 5 [FW_B-Dialer1] dialer-group 10 [FW_B-Dialer1] ip address ppp-negotiate [FW_B-Dialer1] ppp chap user dialeruser2 [FW_B-Dialer1] ppp chap password cipher Hello123 [FW_B-Dialer1] quit [FW_B] firewall zone untrust [FW_B-zone-untrust] add interface Dialer 1 [FW_B-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_B-zone-untrust] quit [FW_B] interface gigabitethernet 1 / 0 / 1 [FW_B-GigabitEthernet1/0/1] pppoe-client dial-bundle-number 5 [FW_B-GigabitEthernet1/0/1] quit 复制代码
[FW_B] dialer-rule 10 ip permit [FW_B] interface Dialer 1 [FW_B-Dialer1] dialer user dialeruser [FW_B-Dialer1] dialer bundle 5 [FW_B-Dialer1] dialer-group 10 [FW_B-Dialer1] ip address ppp-negotiate [FW_B-Dialer1] ppp chap user dialeruser2 [FW_B-Dialer1] ppp chap password cipher Hello123 [FW_B-Dialer1] quit [FW_B] firewall zone untrust [FW_B-zone-untrust] add interface Dialer 1 [FW_B-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_B-zone-untrust] quit [FW_B] interface gigabitethernet 1 / 0 / 1 [FW_B-GigabitEthernet1/0/1] pppoe-client dial-bundle-number 5 [FW_B-GigabitEthernet1/0/1] quit 复制代码
[FW_B] dialer-rule 10 ip permit [FW_B] interface Dialer 1 [FW_B-Dialer1] dialer user dialeruser [FW_B-Dialer1] dialer bundle 5 [FW_B-Dialer1] dialer-group 10 [FW_B-Dialer1] ip address ppp-negotiate [FW_B-Dialer1] ppp chap user dialeruser2 [FW_B-Dialer1] ppp chap password cipher Hello123 [FW_B-Dialer1] quit [FW_B] firewall zone untrust [FW_B-zone-untrust] add interface Dialer 1 [FW_B-zone-untrust] add interface gigabitethernet 1 / 0 / 1 [FW_B-zone-untrust] quit [FW_B] interface gigabitethernet 1 / 0 / 1 [FW_B-GigabitEthernet1/0/1] pppoe-client dial-bundle-number 5 [FW_B-GigabitEthernet1/0/1] quit 复制代码 - 配置Trust域与Untrust域之间的域间安全策略。
-
[FW_B] security-policy [FW_B-policy-security] rule name policy1 [FW_B-policy-security-rule-policy1] source-zone trust [FW_B-policy-security-rule-policy1] destination-zone untrust [FW_B-policy-security-rule-policy1] source-address 10.1.2.0 24 [FW_B-policy-security-rule-policy1] destination-address 10.1.1.0 24 [FW_B-policy-security-rule-policy1] action permit [FW_B-policy-security-rule-policy1] quit [FW_B-policy-security] rule name policy2 [FW_B-policy-security-rule-policy2] source-zone untrust [FW_B-policy-security-rule-policy2] destination-zone trust [FW_B-policy-security-rule-policy2] source-address 10.1.1.0 24 [FW_B-policy-security-rule-policy2] destination-address 10.1.2.0 24 [FW_B-policy-security-rule-policy2] action permit [FW_B-policy-security-rule-policy2] quit 复制代码
[FW_B] security-policy [FW_B-policy-security] rule name policy1 [FW_B-policy-security-rule-policy1] source-zone trust [FW_B-policy-security-rule-policy1] destination-zone untrust [FW_B-policy-security-rule-policy1] source-address 10.1.2.0 24 [FW_B-policy-security-rule-policy1] destination-address 10.1.1.0 24 [FW_B-policy-security-rule-policy1] action permit [FW_B-policy-security-rule-policy1] quit [FW_B-policy-security] rule name policy2 [FW_B-policy-security-rule-policy2] source-zone untrust [FW_B-policy-security-rule-policy2] destination-zone trust [FW_B-policy-security-rule-policy2] source-address 10.1.1.0 24 [FW_B-policy-security-rule-policy2] destination-address 10.1.2.0 24 [FW_B-policy-security-rule-policy2] action permit [FW_B-policy-security-rule-policy2] quit 复制代码
[FW_B] security-policy [FW_B-policy-security] rule name policy1 [FW_B-policy-security-rule-policy1] source-zone trust [FW_B-policy-security-rule-policy1] destination-zone untrust [FW_B-policy-security-rule-policy1] source-address 10.1.2.0 24 [FW_B-policy-security-rule-policy1] destination-address 10.1.1.0 24 [FW_B-policy-security-rule-policy1] action permit [FW_B-policy-security-rule-policy1] quit [FW_B-policy-security] rule name policy2 [FW_B-policy-security-rule-policy2] source-zone untrust [FW_B-policy-security-rule-policy2] destination-zone trust [FW_B-policy-security-rule-policy2] source-address 10.1.1.0 24 [FW_B-policy-security-rule-policy2] destination-address 10.1.2.0 24 [FW_B-policy-security-rule-policy2] action permit [FW_B-policy-security-rule-policy2] quit 复制代码 - 配置Untrust域与Local域之间的域间安全策略。
-
[FW_B-policy-security] rule name policy3 [FW_B-policy-security-rule-policy3] source-zone local [FW_B-policy-security-rule-policy3] destination-zone untrust [FW_B-policy-security-rule-policy3] action permit [FW_B-policy-security-rule-policy3] quit [FW_B-policy-security] rule name policy4 [FW_B-policy-security-rule-policy4] source-zone untrust [FW_B-policy-security-rule-policy4] destination-zone local [FW_B-policy-security-rule-policy4] action permit [FW_B-policy-security-rule-policy4] quit [FW_B-policy-security] quit 复制代码
[FW_B-policy-security] rule name policy3 [FW_B-policy-security-rule-policy3] source-zone local [FW_B-policy-security-rule-policy3] destination-zone untrust [FW_B-policy-security-rule-policy3] action permit [FW_B-policy-security-rule-policy3] quit [FW_B-policy-security] rule name policy4 [FW_B-policy-security-rule-policy4] source-zone untrust [FW_B-policy-security-rule-policy4] destination-zone local [FW_B-policy-security-rule-policy4] action permit [FW_B-policy-security-rule-policy4] quit [FW_B-policy-security] quit 复制代码
[FW_B-policy-security] rule name policy3 [FW_B-policy-security-rule-policy3] source-zone local [FW_B-policy-security-rule-policy3] destination-zone untrust [FW_B-policy-security-rule-policy3] action permit [FW_B-policy-security-rule-policy3] quit [FW_B-policy-security] rule name policy4 [FW_B-policy-security-rule-policy4] source-zone untrust [FW_B-policy-security-rule-policy4] destination-zone local [FW_B-policy-security-rule-policy4] action permit [FW_B-policy-security-rule-policy4] quit [FW_B-policy-security] quit 复制代码 - 配置到达总部和其他私网的静态路由。
-
[FW_B] ip route- static 0.0.0.0 0.0.0.0 Dialer1 复制代码
[FW_B] ip route- static 0.0.0.0 0.0.0.0 Dialer1 复制代码
[FW_B] ip route- static 0.0.0.0 0.0.0.0 Dialer1 复制代码
-
-
在FW_B上配置IPSec策略,并在接口上应用IPSec策略。
- 定义被保护的数据流。
-
[FW_B] acl 3000 [FW_B-acl-adv-3000] rule permit ip source 10.1.2.0 0.0.0.255 destination 10.1.0.0 0.0.255.255 [FW_B-acl-adv-3000] quit 复制代码
[FW_B] acl 3000 [FW_B-acl-adv-3000] rule permit ip source 10.1.2.0 0.0.0.255 destination 10.1.0.0 0.0.255.255 [FW_B-acl-adv-3000] quit 复制代码
[FW_B] acl 3000 [FW_B-acl-adv-3000] rule permit ip source 10.1.2.0 0.0.0.255 destination 10.1.0.0 0.0.255.255 [FW_B-acl-adv-3000] quit 复制代码 - 配置名称为tran1的IPSec安全提议。采用默认参数。
-
[FW_B] ipsec proposal tran1 [FW_B-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_B-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_B-ipsec-proposal-tran1] quit 复制代码
[FW_B] ipsec proposal tran1 [FW_B-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_B-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_B-ipsec-proposal-tran1] quit 复制代码
[FW_B] ipsec proposal tran1 [FW_B-ipsec-proposal-tran1] esp authentication-algorithm sha2- 256 [FW_B-ipsec-proposal-tran1] esp encryption-algorithm aes- 256 [FW_B-ipsec-proposal-tran1] quit 复制代码 - 配置序号为10的IKE安全提议。采用默认参数。
-
[FW_B] ike proposal 10 [FW_B-ike-proposal-10] authentication-method pre-share [FW_B-ike-proposal-10] prf hmac-sha2- 256 [FW_B-ike-proposal-10] encryption-algorithm aes- 256 [FW_B-ike-proposal-10] dh group2 [FW_B-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_B-ike-proposal-10] quit 复制代码
[FW_B] ike proposal 10 [FW_B-ike-proposal-10] authentication-method pre-share [FW_B-ike-proposal-10] prf hmac-sha2- 256 [FW_B-ike-proposal-10] encryption-algorithm aes- 256 [FW_B-ike-proposal-10] dh group2 [FW_B-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_B-ike-proposal-10] quit 复制代码
[FW_B] ike proposal 10 [FW_B-ike-proposal-10] authentication-method pre-share [FW_B-ike-proposal-10] prf hmac-sha2- 256 [FW_B-ike-proposal-10] encryption-algorithm aes- 256 [FW_B-ike-proposal-10] dh group2 [FW_B-ike-proposal-10] integrity-algorithm hmac-sha2- 256 [FW_B-ike-proposal-10] quit 复制代码 - 配置IKE Peer。
-
[FW_B] ike peer a [FW_B-ike-peer-a] ike-proposal 10 [FW_B-ike-peer-a] remote-domain www. abcd .3322 . org [FW_B-ike-peer-a] pre-shared-key Test ! 1234 [FW_B-ike-peer-a] quit 复制代码
[FW_B] ike peer a [FW_B-ike-peer-a] ike-proposal 10 [FW_B-ike-peer-a] remote-domain www. abcd .3322 . org [FW_B-ike-peer-a] pre-shared-key Test ! 1234 [FW_B-ike-peer-a] quit 复制代码
[FW_B] ike peer a [FW_B-ike-peer-a] ike-proposal 10 [FW_B-ike-peer-a] remote-domain www. abcd .3322 . org [FW_B-ike-peer-a] pre-shared-key Test ! 1234 [FW_B-ike-peer-a] quit 复制代码 - 配置名称为map1序号为10的IPSec策略。
-
[FW_B] ipsec policy map1 10 isakmp [FW_B-ipsec-policy-isakmp-map1-10] security acl 3000 [FW_B-ipsec-policy-isakmp-map1-10] proposal tran1 [FW_B-ipsec-policy-isakmp-map1-10] ike-peer a [FW_B-ipsec-policy-isakmp-map1-10] quit 复制代码
[FW_B] ipsec policy map1 10 isakmp [FW_B-ipsec-policy-isakmp-map1-10] security acl 3000 [FW_B-ipsec-policy-isakmp-map1-10] proposal tran1 [FW_B-ipsec-policy-isakmp-map1-10] ike-peer a [FW_B-ipsec-policy-isakmp-map1-10] quit 复制代码
[FW_B] ipsec policy map1 10 isakmp [FW_B-ipsec-policy-isakmp-map1-10] security acl 3000 [FW_B-ipsec-policy-isakmp-map1-10] proposal tran1 [FW_B-ipsec-policy-isakmp-map1-10] ike-peer a [FW_B-ipsec-policy-isakmp-map1-10] quit 复制代码 - 在Dialer 1接口上应用IPSec策略map1。
-
[FW_B] interface Dialer 1 [FW_B-Dialer1] ipsec policy map1 [FW_B-Dialer1] quit 复制代码
[FW_B] interface Dialer 1 [FW_B-Dialer1] ipsec policy map1 [FW_B-Dialer1] quit 复制代码
[FW_B] interface Dialer 1 [FW_B-Dialer1] ipsec policy map1 [FW_B-Dialer1] quit 复制代码
- 在FW_B上配置DNS。
[FW_B] ip host dns_ipsec 3.3.3.3 复制代码[FW_B] ip host dns_ipsec 3.3.3.3 复制代码[FW_B] ip host dns_ipsec 3.3.3.3 复制代码
- 配置FW_C。
请参见FW_B的配置。
原文链接:https://blog.csdn.net/guolianggsta/article/details/127214748?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522168449620216800188544320%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=168449620216800188544320&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2~blog~first_rank_ecpm_v1~times_rank-19-127214748-null-null.blog_rank_default&utm_term=NAS%E3%80%81%E7%BE%A4%E6%99%96%E3%80%81%E9%98%BF%E9%87%8C%E4%BA%91%E3%80%81%E5%9F%9F%E5%90%8D%E8%A7%A3%E6%9E%90%E3%80%81%E5%86%85%E7%BD%91%E7%A9%BF%E9%80%8F%E3%80%81ipv6%E3%80%81ddns%E3%80%81%E8%BD%BB%E9%87%8F%E7%BA%A7%E4%BA%91%E6%9C%8D%E5%8A%A1%E5%99%A8%E3%80%81%E9%93%81%E5%A8%81%E9%A9%AC%E3%80%81%E5%A8%81%E8%81%94%E9%80%9A%E3%80%81DSM%E3%80%81DSM6.0%E3%80%81%E7%BE%A4%E6%99%96nas%E3%80%81%E4%BA%91%E6%9C%8D%E5%8A%A1%E5%99%A8%E3%80%81%E8%9C%97%E7%89%9B%E6%98%9F%E9%99%85%E3%80%81%E9%BB%91%E7%BE%A4%E6%99%96%E3%80%81docker%E3%80%81%E5%AE%B9%E5%99%A8%E9%95%9C%E5%83%8F%E3%80%81%E5%9F%9F%E5%90%8D%E6%B3%A8%E5%86%8C%E3%80%81%E5%AE%9D%E5%A1%94%E3%80%81%E5%8F%8D%E5%90%91%E4%BB%A3%E7%90%86%E3%80%81nginx%E3%80%81frp%E3%80%81%E5%8A%A8%E6%80%81%E5%9F%9F%E5%90%8D%E8%A7%A3%E6%9E%90